Keeping your payments safe: your guide to payments and transaction rulesGuard your B2B payments against fraud with confidence
Guide
Why does payment processing matter for businesses?
Payment fraud is a big problem for companies of all industries, shapes and sizes. Risk teams are growing increasingly concerned over the evolving payment fraud landscape, struggling to protect on all fronts when it comes to cyber threats.
You can improve confidence in your payments by understanding how the regulations are set up to protect you, and how you can take this further with automated bank verification.
Confidence – how much of it do you really have in the payments your business makes and receives?
Every team member, from payments administrators to the CFO, is under pressure to step and apply their expertise to payment processing.
Fortunately, the regulations, like PSD2, were built to help you detect suspicious activity in direct debit verification. By honing in on the technical specifications of these systems, you can learn the rules and take the reins to make sure that your organisation’s funds don’t end up in the wrong hands.
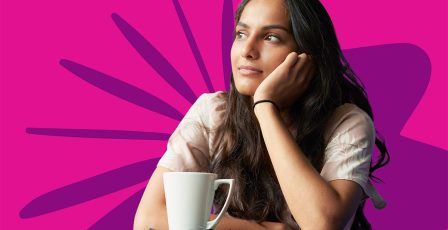
Payment systems for businesses
A payment system involves a group of participants that enable the transfer of funds electronically between individuals, businesses and financial institutions. In a corporate setting, you’ll most commonly rely on payment systems to accept online payments from customers, pay out to suppliers, and manage internal transfers.
Payment systems lay out a set of shared standards that are upheld by each of the participants. This includes:
- Banks
- Payment service providers (PSPs)
- Third party service providers: innovative financial-adjacent services, such as budgeting tools, subscription finders and point of sale hosts
At the end of a successful payment system is a settlement: the payment made.
This guide covers the rules that make settlements possible, including a breakdown of validation and verification methods to keep your payments safe, and delivered to the correct recipient.
The requirements ensure that confidential personal and transaction information remains secure, enabling payments to be made safely. However, the rules also exist to protect the participants against impersonators who falsely claim to be suppliers, customers or other parties.
How could fraudsters manipulate payment systems to access money?
One of the most common examples of a B2B payments scam is a phishing email which appears to be from a legitimate vendor.

This ‘password change’ notification aims to spark panic in the reader, as it’s a completely false narrative.
The cyberattackers’ aim is that:
- The reader, typically a finance administrator or senior figure at the victim organisation, clicks through to the spoofed site on the other end.
- The victim inputs their current password to ‘change’ it.
- The cyberattackers capture this information (the real credentials).
- The fraudster logs into the system using the real credentials, either accessing confidential information, reviewing real suppliers to later create fake invoices, or directly making payments to themselves.
And if even huge global brands like Microsoft can be targeted, so can all businesses.
In fact, between 2023 and 2024, over 60% of businesses[1] reported being in the press or social media due to fraud. The negative reputational impacts of scams like this have caused companies to lose trust, clients, and revenue.
Fortunately, regulatory standards like PSD2 are catching up with these types of scams, and payment systems now have built-in defence mechanisms to protect your business’ bank accounts, even if other departments, such as email accounts, are compromised.
Key Takeaway
Fraudsters target vulnerabilities in electronic payments by manipulating payers and impersonating recipients. It’s the responsibility of all payment systems participants to uphold the integrity of these transactions by putting in measures to detect suspicious activity.
BACS Direct Debit and SEPA: what are the rules?
There are dozens of different domestic and international electronic payments systems in the UK, but BACS and SEPA are two of the most popular[2] systems for sending paperless direct debits.
The rules are simple for both of these systems:
Payment Service Providers (PSPs) must conduct checks at various stages before settling a payment. To do this, PSPs work with BACS or SEPA to access information about specific bank accounts to complete these checks.before payment is settled, PSPs are required to perform checks at different stages of the journey. PSPs partner with BACS or SEPA to get the information that the system holds about specific bank accounts in order to complete these checks.
Once the direct debit verification checks are complete, the payment service provider will receive an information message, such as “This account is valid for SEPA payments” or “This account is not valid for SEPA payments.”
What is BACS Direct Debit?
BACS (Bankers’ Automated Clearing Services) is payment system used for processing direct debits and credits within the UK. It enables the secure transfer of funds between bank accounts, ensuring payments are made from one account to another.
Over 1.6 billion BACS direct debit payments[3] were sent in Q1 of 2024, making it one of the most popular ways to pay electronically in the UK.
Businesses typically encounter BACS direct debits when paying regular bills, such as office rent, utilities, or payroll. Businesses can also collect Direct Debits from customers, which automates the regular collection of payments. This is especially useful for subscription business models.
What is SEPA 2?
SEPA (Single Euro Payments Area) is a framework that governs international payments within the eurozone. It was updated to SEPA 2, which now requires both IBANs and Business Identifier Codes (BICs) due to the 2.2% error rate associated with relying solely on IBANs.
SEPA incorporates all 27 European Union member states, plus nine further countries including the United Kingdom. At Experian, we understand the global nature of the marketplace and offer banking information validation in 75 countries, including those in the SEPA region.
The direct debit guarantee refers to the fact that customers, including business customers, are entitled to a full refund if an error is made by the bank or payment service provider. Any participant that facilitates direct debit payment must adhere to the direct debit refund guarantee, thus improving confidence in the payment method across all networks.
BIC stands for Business Identifier Code, formerly Bank Identifier Code. It is a crucial piece of information used to identify a bank in international transactions.
11–character BIC and SWIFT codes are the same and interchangeable (SWIFT is just the system that manages BIC). This means that payment system participants can use either to ensure that payments are going to the right account.
If you need to find BIC payment information, get a free trial of Bank Wizard to validate bank account data, and convert the IBAN into a BIC.
IBAN stands for International Bank Account Number and is a unique identifier for an individual bank account used in international transactions.
STP means straight through processing, which enables system participants to remove manual intervention and automate parts of the payment process to speed it up. Bank verification solutions help payers to improve their STP rates by streamlining verification and highlighting errors upfront.
Key Takeaway
BACS is a domestic payment system in the UK, while SEPA is an international payment system across Europe. Both systems have specific rules that participants must follow to ensure payments are directed to the correct accounts
Validate, verify and confirm payments
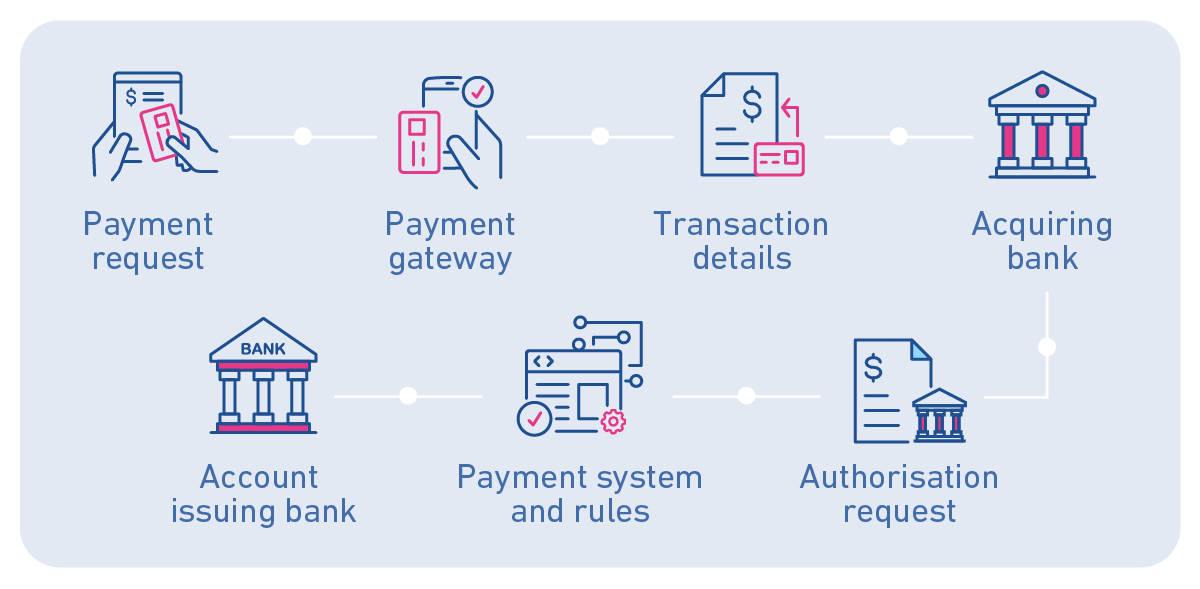
There are three core stages to the Experian payment process involving direct debit scheme rules:
- Validation (Bank Wizard)
- Verification
- Confirmation of Payee
Validation
Bank account validation is the process of confirming the accuracy of an entered bank account number. It ensures that the administrator hasn’t mis–keyed any of the data, and that the account number and sort code are in the correct format.
The primary benefit of this step is the ability to correct any errors in real time while still in contact with the customer.
Rather than discovering a mistake after a failed direct debit in 25 days, for example, you can identify and fix the error immediately, reducing the number of rejected payments.
The first stage is validation, using the BACS system if the payment is UK-based or SWIFT to obtain SEPA information if it’s an international payment. Experian’s Bank Wizard Absolute detects errors when capturing and processing account and card details. It uses the Extended Industry Sort Code Directory to access UK sort codes and applies BACS rules to ensure account numbers are in the correct format.
Verification
Bank account verification is the process of confirming that a bank account is valid, active, and owned by the individual or entity claiming ownership. The second stage serves. This stage basically answers, does this bank account exist?
Verification is important for flagging suspicious accounts, allowing your team to investigate further before falling victim to payment fraud.
Finance teams can set automated rules to block payments to accounts with high-risk scores or mismatched information, ensuring they are fully verified before any funds are transferred.
We then verify that the account details actually exist using BACS rules. We check the Experian Bureau to confirm the existence of the sort code and account number. The record will also include the name, date of birth, and address. We provide a risk score based on how closely the details match and flag potential risks, such as the age of the account or whether it is a joint or single account.
Confirmation of Payee (CoP)
Confirmation of Payee (CoP) is a process used to verify that the name of the account holder matches the account details provided when making a payment. If you’ve sent a payment using online banking in the UK within the last few years – you might already be familiar with CoP without realising it!

In the past, when making a payment to a new person or business, the sender only needed to enter the sort code and account number. Now, they must also provide the name of the recipient as an additional verification step.
This extra check is especially useful for preventing impersonation fraud, as fraudsters often use false names that CoP checks can flag.
All UK payment service providers were required to start adhering to CoP in October 2024, but this isn’t a required standard for overseas transactions.
The latest update to the BACS Service Users Guide and Rules includes new requirements for setting up direct debits. One important change (Section 3b), is the need to verify not only the sort code and account number, but also the account name and address. Our solution is designed to check all of this information, ensuring it meets the updated requirements. This provides our clients with confidence that the account details match and payments are being sent to the correct recipient.
Key Takeaway
Payers and payees can be authenticated through validation, checking that there are no errors in formatting; through verification, checking that the account truly exists; and through confirmation, ensuring that the data matches and the person or business is who they say they are.
Fraud: the payments and transactions challenge
Payment systems exist to promote high security standards and keep payments safe. However, as virtually all B2B payments now occur online, rather than in cash, these systems have become a key target for cyberattackers.
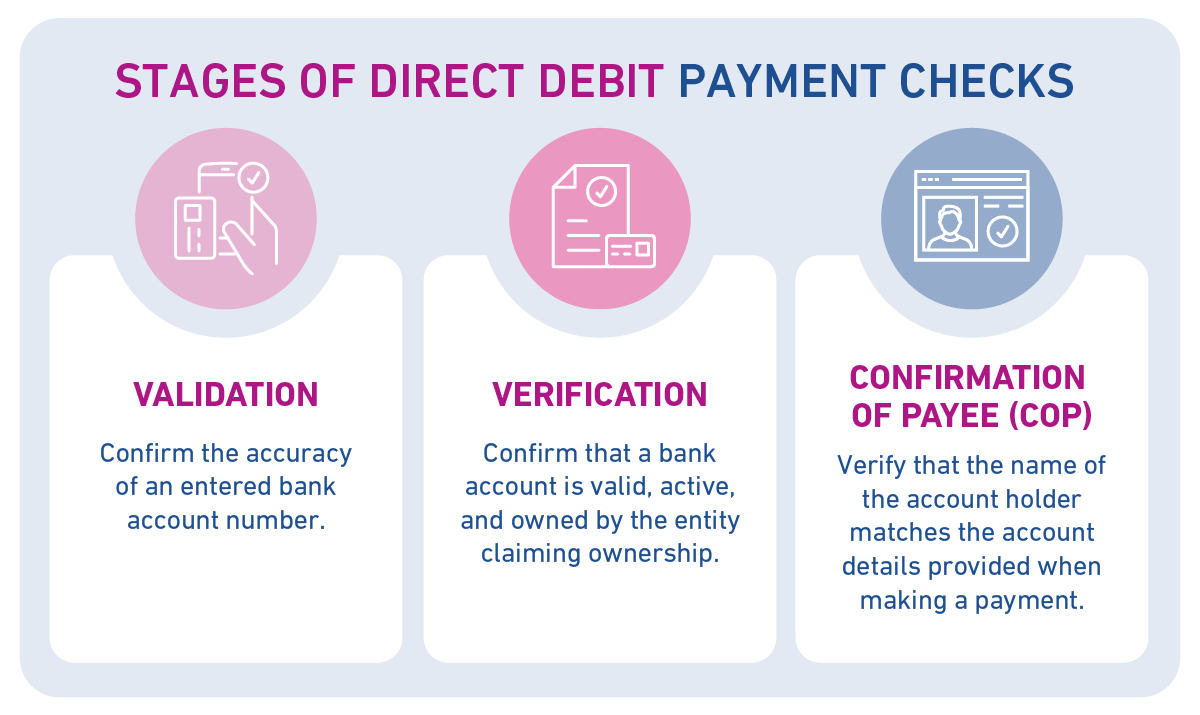
Card not present transactions: risky but no alternative
Card not present transactions, as known as paperless direct debits, happen when the cardholder, card and merchant are not all in the same place. Card not present transactions increase the fraud risks associated with making payments.
The table below shows examples of card not present transactions and their fraud risks:
| Type | Description | Fraud Risks |
| Online payments | The cardholder enters their card details online through an API, and the merchant usually receives the funds without seeing the payment details. | Without multi-factor authentication, it’s difficult for merchants to verify that the payee is the legitimate cardholder. This increases the risk of chargebacks. |
| Payments over the phone | The cardholder reads their card details over the phone, and the merchant manually inputs them into the payment device. | The lack of automatic verification makes customer authentication challenging. A solution is to cross-check the telephone number against your records. |
| Mail order | The cardholder fills out a paper order form and provides their signature to verify their identity and account information. | The merchant must contact the payee if a CVV check is needed, which is time-consuming and manual. |
| Card on file | Used for repeat purchases where amounts vary, and card information is retained for easy checkout. | In addition to authentication concerns, there are risks if the card expires, requiring the merchant to update details or seek alternative payment methods. |
| Cloud wallets | The cardholder uses a mobile app (e.g., Apple Pay) to pay, without the physical card being present, often in the same location as the merchant. | This is a more secure payment method as it typically requires face ID, making it harder for fraudsters to bypass. |
Key Takeaway
Unfortunately, the risk of fraud in payments is increasing. Despite this, online payments remain the preferred choice for businesses, as they offer reduced admin and collection time.
Securing payments with PSD2 regulations
Thankfully, the payment systems rules for BACS were updated with the incoming second iteration of the Payment Services Directive – an EU and UK regulatory framework. These requirements aim to reduce the risks of payment fraud cases, especially in card not present transactions.
Both PSD2 and BACS compliance help to secure a BACS direct debit payment.
What is PSD2?
PSD2 (Payment Services Directive 2) is an updated regulation, introduced in 2018,that established a set of standards for payment services providers across Europe. Its primary goals are to enhance the security of digital payments and open the market to third-party fintech companies, which were previously viewed with public skepticism due to a lack of regulation.
An added benefit of PSD2 is increased competition, forcing large, established companies to innovate to keep up with newer tech companies that are improving the customer experience.
Implementation of PSD2
The implementation of PSD2 included the introduction of Strong Customer Authentication (SCA).
SCA improves the security of payments across any UK network by requiring PSPs to verify at least two of the following three factors:
- Inherence: something the user is: biometrics like facial ID or fingerprint.
- Knowledge: something the user knows: passwords or chosen questions (such as, what is your mothers maiden name?).
- Possession: something the user has: a code sent to a mobile phone or email account known to be associated with the account holder.
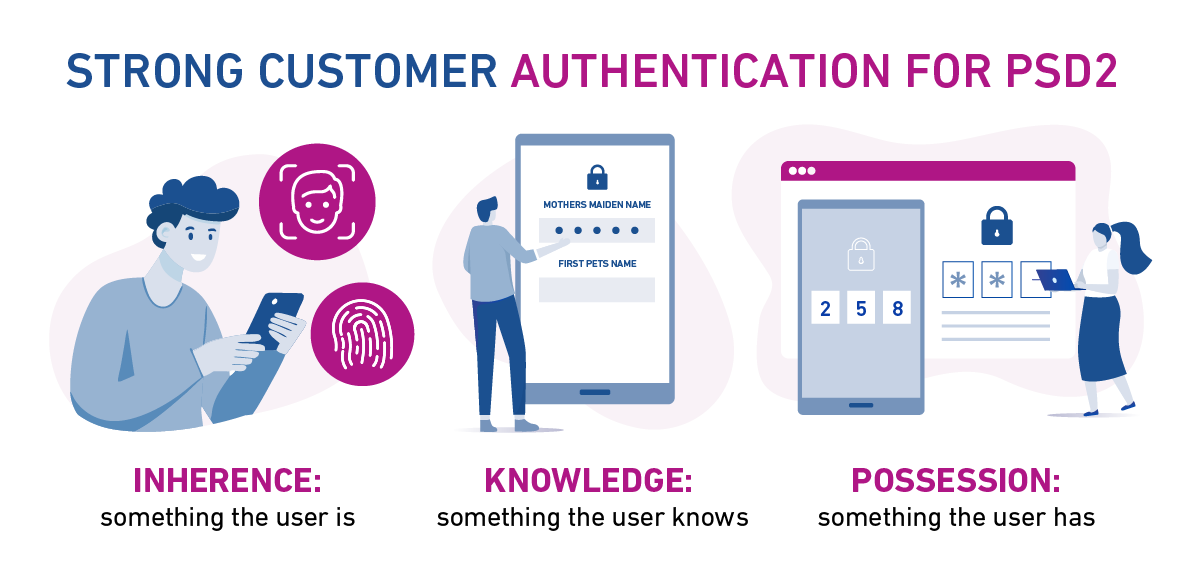
Thanks to PSD2, we now see widespread use of two factor authentication methods to complete SCA.
Other key implementation changes[4] included:
- Transaction monitoring to detect suspicious payments activity faster and with better accuracy
- The introduction of standardisation for APIs which would enable third parties to enter payments networks securely
Impacts of PSD2 on payment services
PSPs Payment Service Providers (PSPs) were forced to improve the way that they authenticated their customers, especially with third parties now involved. As a result, products required a higher level of verification.In terms of how that actually impacted the products, it meant that a greater level of verification became required. You can’t get away with just taking the bank details to make a payment anymore, : PSPs need to perform a verification check.
It’s fair to say that PSD2 has transformed the finance industry, opening the door to smarter budgeting, automatic bill payments and intuitive new services. But it’s from a security point of view that PDS2 has had the biggest impact.
Key Takeaway
PSD2 goes beyond simply confirming the data is formatted correctly, requiring participants to confirm the account:
- is active (not closed or owned by a deceased person)
- is associated with the person providing the details.
How can we help?
By placing bank account verification at the heart of your organisation, Experian can help you not only avoid the negative reputational impacts of payment fraud, but the monetary consequences as well.
Glide through day–to–day financial operations without having to manually input and verify the data, reducing each of the risks associated with electronic payments.
For more information on automating the bank account verification process, talk to an expert.
[1] The reputational cost of fraud and its impact on brand image – the latest figures revealed, Ravelin
[2] Quarterly Statistical Report, Pay.UK
[3] Quarterly Statistical Report, Pay.UK
[4] The revised Payment Services Directive (PSD2) and the transition to stronger payments security, European Central Bank